New Default Accounts for Windows
Dear  JDisc friends,
JDisc friends,
today, I would like to cover a topic which has been causing questions and problems for quite a while. Today, we are talking about how to configure Windows accounts in order to scan Windows servers and clients.
JDisc Discovery always tries to minimize login attempts with username/password pairs. Otherwise intrusion detection systems might create alerts when there are login attempts with too many username/passwords.
For Windows computers, JDisc Discovery uses mainly Windows domain and AD accounts. Therefore, in the first phase of the device discovery, we try to determine the Windows domain and the Active Directory OU (organizational unit) to which a device belongs to. If we find either the Windows domain or the OU, then we can use the administrative account which was configured for the domain or the OU for the deep device scan.
While the approach described above works for most environments, there are some situations, where we are not able to get the domain or the OU. In this case, we will not be able to find an administrative account for the deep scan. The device will only return little or no information.
But wait a minute. There are default accounts for Linux, VMware, HP-UX, Solaris and other Unix based operating systems. Why not add a new tab with default accounts tab for Windows?
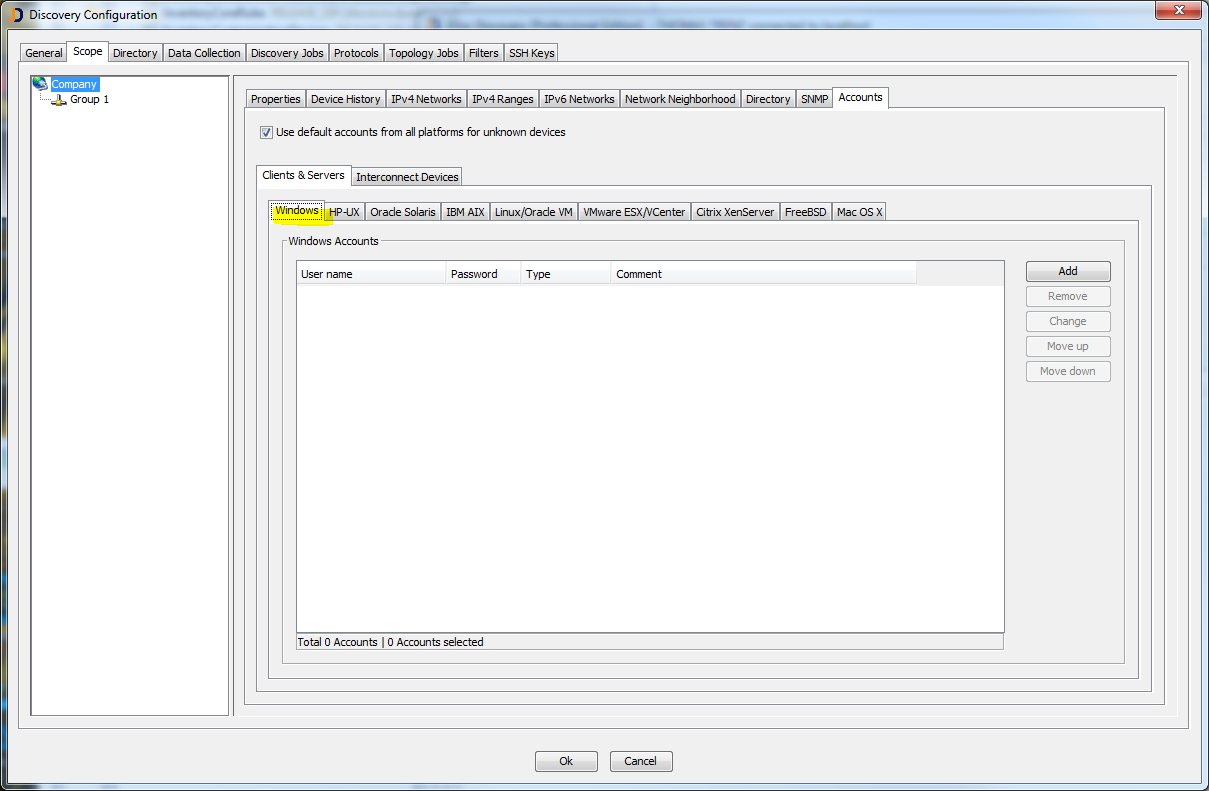
New: Windows Default Accounts
We changed the configuration dialog in order to provide a tab for Windows default accounts. The default accounts will be tested when no domain or active directory account succeeded.
But one important comment from our side. The default accounts are the always the last option to define Windows administrative accounts. Use them only, if you can’t get the Windows computers using domain or active directory accounts.
Otherwise intrusion detection systems might create alerts!
Hope this feature helps in some situations to get the proper data for Windows computers.
This feature will be part of the JDisc Discovery product starting with build 3363 which will be released on Dec-12 2016.
Cheers,
Thomas

